mirror of
https://github.com/KANIKIG/Multi-EasyGost.git
synced 2025-08-10 00:52:32 +00:00
first commit
This commit is contained in:
110
README.md
Executable file
110
README.md
Executable file
@@ -0,0 +1,110 @@
|
||||
# GOST一键脚本使用指南
|
||||
***
|
||||
#### 感谢:
|
||||
1. 感谢 @ginuerzh 大佬提供了如此优秀实用的软件,项目地址 `https://github.com/ginuerzh/gost` ,GOST功能强大使用简单,想要详细了解用法的朋友可以查看官方文档 `https://docs.ginuerzh.xyz/gost/`
|
||||
2. 感谢 @风萧萧兮易水寒 大佬的原始脚本,本脚本的灵感与思路都来自此大佬的一键脚本,项目地址 `https://www.fiisi.com/?p=125`
|
||||
***
|
||||
> 脚本简介
|
||||
> > 适合懒人的超简单gost一键转发脚本:
|
||||
> > `wget --no-check-certificate -O gost.sh https://raw.githubusercontent.com/KANIKIG/EasyGost/master/gost.sh && chmod +x gost.sh && ./gost.sh`
|
||||
> > 脚本由 @stsdustjc 制作,参考了 @风萧萧兮易水寒 大佬的一键脚本,主要实现了systemd及gost配置文件对gost进行管理,能够在不借助其他工具(如screen)的情况下实现多条转发规则同时生效。但功能性较弱,目前仅支持tcp+udp不加密转发, relay+tls加密转发, relay+tls解密对接转发。也算是能勉强保护一下裸奔的流量和搭建简单隧道的需求了。
|
||||
> > 项目地址及帮助文档:
|
||||
> > https://github.com/KANIKIG/EasyGost
|
||||
***
|
||||
## 本一键脚本适用人群
|
||||
* 你只是想赶快用上gost进行流量转发,不想学习gost的详细配置方法,只想越简单越好
|
||||
* 你对转发的要求并不高,纯转发或简单加密就能满足要求了
|
||||
* 在满足上一条的情况下,你可能有多项gost转发规则,想要管理起来方便些
|
||||
##### 如果你不符合上述条件请自行阅读gost的官方文档,gost能够通过简单的命令实现非常多强大的功能,但本脚本并未加入那些功能
|
||||
##### 如果你是萌新,有很多与IP/端口/转发有关的概念都还没弄清楚,请跟随本文的「完整食用教程」一步步进行设置,最终通过一键脚本实现转发
|
||||
|
||||
***
|
||||
## 完整食用教程
|
||||
* 启动脚本: 在已经运行过如下一键脚本的情况下
|
||||
`wget --no-check-certificate -O gost.sh https://raw.githubusercontent.com/KANIKIG/EasyGost/master/gost.sh && chmod +x gost.sh && ./gost.sh`
|
||||
* 再次运行本脚本只需要输入`./gost.sh`回车即可
|
||||
|
||||
***
|
||||
|
||||
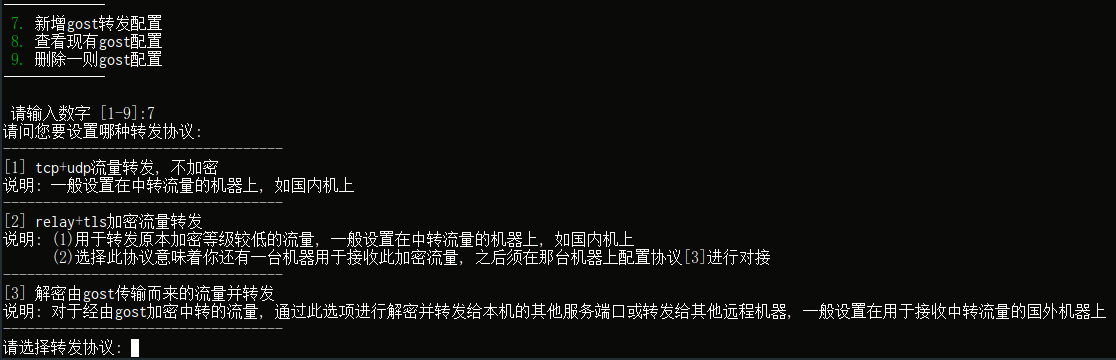
* 难点1: 协议选择
|
||||
|
||||
* 对于具备足够加密强度的流量,如某些服务(Caddy, Nginx)提供的tls加密,这种情况下你可能只需要对流量进行中转而不需要加密,那么选[1]即可,在这种情况下,你只需要配置一台主机(中转流量的主机)即可实现GOST转发流量
|
||||
* 有一些服务的加密强度是不可靠的,所以你希望通过GOST实现在中转流量的同时对流量进行加密,这种情况下选[2]即可。值得说明的是:
|
||||
- 当选择[2]对中转流量进行加密时,意味着你还需要配置你的远程主机,即接收这些转发流量的主机,需要登录上远程主机运行此脚本,并选择协议[3]对来自于此主机的加密流量进行解密,从而供远程主机的其他服务接收这些流量
|
||||
- 目前本脚本仅采用GOST提供的默认证书,亦可能受到HTTPS中间人攻击,如果想要更加安全,请放弃使用此脚本,自行学习GOST官方文档
|
||||
* 协议[3]用于接收通过[2]转发而来的加密流量,即如果中转主机使用了协议[2],则要在对应的目标主机上选择协议[3]以对接
|
||||
|
||||
***
|
||||
|
||||
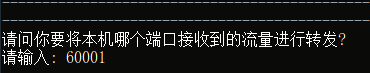
* 难点2: 本地端口填写
|
||||

|
||||
|
||||
* 本地端口是指,当前正在使用脚本的这台主机要监听的端口,从这个端口注入的流量会经由GOST服务进行处理(转发/加密/解密)
|
||||
* 一般而言,如果使用国内的NAT类机型,分为外网和内网两种端口,这里应填内网端口(如图60001)
|
||||
* 而外部的其他客户端想要连接到这一台NAT主机时则需要在外部的客户端上填写外网端口(37096)以实现端口映射和连接,当然这一部分与本脚本无关,外部端口也无需在本脚本中填写
|
||||
* 一般而言,对于有独立IP的VPS/VDS/独服等类型的主机,端口通常都是全开放的,这里的端口直接自己按需填写即可,不存在内外之分(建议填写10000号以上的端口)
|
||||
|
||||
***
|
||||
|
||||
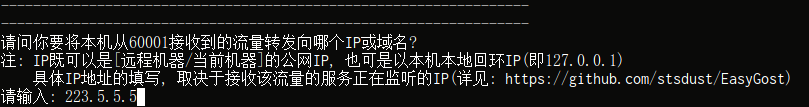
* 难点3: IP填写
|
||||
- IP填写分为几种情况,这里按3种协议选项进行解释
|
||||
- [A]---[B]---[C],假如A是你自己正在用的电脑,[B]是用于转发流量的主机,[C]是最终接收由[A]发出流量的主机
|
||||
1. 选择协议[1]的,即不加密的流量转发,则此处填写你[C]主机的IP即可
|
||||
2. 在[B]主机上选择协议[2]的,即对流量进行加密,则此处也是填写[C]主机的IP,如图:
|
||||
|
||||
3. 在[C]主机上选择协议[3]的,即对由[B]转发过来的流量进行解密,则此处填写[C]主机的IP或`127.0.0.1`,这取决于在[C]主机上,GOST接收到这些流量后要将流量交给[C]主机面向外部的端口,还是面向[C]主机内部本地回环的端口
|
||||
* 一般来讲,只有[A]---[C]的情况下,[C]主机某服务的端口是监听在本机上而非本地回环的,某些服务配置文件一般是这种形式:
|
||||
|
||||
```javascript
|
||||
"server":"0.0.0.0",
|
||||
"local_address":"127.0.0.1",
|
||||
"local_port":22332,
|
||||
```
|
||||
|
||||
* 或者这种形式
|
||||
|
||||
```javascript
|
||||
{
|
||||
"inbounds": [
|
||||
{
|
||||
"port": 22332,
|
||||
"protocol": "?????",
|
||||
"settings": {
|
||||
"clients": [
|
||||
```
|
||||
|
||||
* 以上2种形式的服务端配置文件都表明服务监听在本机的22332端口上,而不是本地回环,这种情况IP填写本机[C]的公网IP即可
|
||||
* 同样的,通过修改你[C]主机上对应服务的配置文件,可以实现让这一服务仅监听在[C]主机本地回环的端口上,如`127.0.0.1:22332`即如下配置所示
|
||||
|
||||
```javascript
|
||||
"server":127.0.0.1",
|
||||
"local_address":"127.0.0.1",
|
||||
"local_port":22332,
|
||||
```
|
||||
|
||||
* 或者这种形式
|
||||
|
||||
```javascript
|
||||
{
|
||||
"inbounds": [
|
||||
{
|
||||
"port": 22332,
|
||||
"listen":"127.0.0.1",
|
||||
"protocol": "?????",
|
||||
"settings": {
|
||||
"clients": [
|
||||
```
|
||||
|
||||
* 以上2种形式的服务端配置文件都表明服务监听在本地回环(127.0.0.1)的22332端口上,换言之,除了本机内部的流量外,其他来源的流量都无法访问这一服务,因此安全系数更高,而GOST恰恰可以把从外部接收来的流量转发至本机内部
|
||||
* 这种情况IP填写为`127.0.0.1`即可
|
||||
|
||||
***
|
||||
|
||||
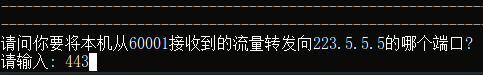
* 难点4: 目标端口填写
|
||||
- 算不上难点,稍微需要注意的地方提示一下
|
||||
|
||||
1. 选择协议[1]的,此处填写你[C]主机对应服务监听的端口即可,可能是`443`也可能是如上示例的`22332`,具体依据目标主机对应服务的配置
|
||||
2. 在[B]主机上选择协议[2]的,则此处建议填写`443`,当然你硬要填写其他的我也拦不住
|
||||
3. 在[C]主机上选择协议[3]的,需要比较注意,在[C]主机上选择协议[3]意味着你[B]主机选的是协议[2],那么[C]主机在用此脚本时第一次填写的本地端口(难点2),应该与[B]主机上配置时填写的目标端口相一致(难点4.2),一般是`443`,而第二次填写的端口应与[C]主机上具体服务所监听的端口相一致,按如上示例即为`22332`
|
||||
|
||||
### 到此一切设置完毕,尽情享受GOST为你带来的便捷吧 :)
|
||||
7
config.json
Executable file
7
config.json
Executable file
@@ -0,0 +1,7 @@
|
||||
{
|
||||
"Debug": true,
|
||||
"Retries": 0,
|
||||
"ServeNodes": [
|
||||
"udp://127.0.0.1:65532"
|
||||
]
|
||||
}
|
||||
13
gost.service
Executable file
13
gost.service
Executable file
@@ -0,0 +1,13 @@
|
||||
[Unit]
|
||||
Description=gost
|
||||
After=network-online.target
|
||||
Wants=network-online.target systemd-networkd-wait-online.service
|
||||
|
||||
[Service]
|
||||
Type=simple
|
||||
User=root
|
||||
DynamicUser=true
|
||||
ExecStart=/usr/bin/gost -C /etc/gost/config.json
|
||||
|
||||
[Install]
|
||||
WantedBy=multi-user.target
|
||||
486
gost.sh
Executable file
486
gost.sh
Executable file
@@ -0,0 +1,486 @@
|
||||
#! /bin/bash
|
||||
Green_font_prefix="\033[32m" && Red_font_prefix="\033[31m" && Green_background_prefix="\033[42;37m" && Red_background_prefix="\033[41;37m" && Font_color_suffix="\033[0m"
|
||||
Info="${Green_font_prefix}[信息]${Font_color_suffix}"
|
||||
Error="${Red_font_prefix}[错误]${Font_color_suffix}"
|
||||
Tip="${Green_font_prefix}[注意]${Font_color_suffix}"
|
||||
gost_conf_path="/etc/gost/config.json"
|
||||
raw_conf_path="/etc/gost/rawconf"
|
||||
function checknew()
|
||||
{
|
||||
checknew=$(gost -V 2>&1|awk '{print $2}')
|
||||
check_new_ver
|
||||
echo "你的gost版本为:"$checknew""
|
||||
echo -n 是否更新\(y/n\)\:
|
||||
read checknewnum
|
||||
if test $checknewnum = "y";then
|
||||
`cp -r /etc/gost /tmp/`
|
||||
Install_ct
|
||||
`rm -rf /etc/gost`
|
||||
`mv /tmp/gost /etc/`
|
||||
`systemctl restart gost`
|
||||
else
|
||||
exit 0
|
||||
fi
|
||||
}
|
||||
function check_sys()
|
||||
{
|
||||
if [[ -f /etc/redhat-release ]]; then
|
||||
release="centos"
|
||||
elif cat /etc/issue | grep -q -E -i "debian"; then
|
||||
release="debian"
|
||||
elif cat /etc/issue | grep -q -E -i "ubuntu"; then
|
||||
release="ubuntu"
|
||||
elif cat /etc/issue | grep -q -E -i "centos|red hat|redhat"; then
|
||||
release="centos"
|
||||
elif cat /proc/version | grep -q -E -i "debian"; then
|
||||
release="debian"
|
||||
elif cat /proc/version | grep -q -E -i "ubuntu"; then
|
||||
release="ubuntu"
|
||||
elif cat /proc/version | grep -q -E -i "centos|red hat|redhat"; then
|
||||
release="centos"
|
||||
fi
|
||||
bit=$(uname -m)
|
||||
if test "$bit" != "x86_64"; then
|
||||
echo "请输入你的芯片架构,/386/armv5/armv6/armv7/armv8"
|
||||
read bit
|
||||
else bit="amd64"
|
||||
fi
|
||||
}
|
||||
function Installation_dependency()
|
||||
{
|
||||
gzip_ver=$(gzip -V)
|
||||
if [[ -z ${gzip_ver} ]]; then
|
||||
if [[ ${release} == "centos" ]]; then
|
||||
yum update
|
||||
yum install -y gzip
|
||||
else
|
||||
apt-get update
|
||||
apt-get install -y gzip
|
||||
fi
|
||||
fi
|
||||
}
|
||||
function check_root()
|
||||
{
|
||||
[[ $EUID != 0 ]] && echo -e "${Error} 当前非ROOT账号(或没有ROOT权限),无法继续操作,请更换ROOT账号或使用 ${Green_background_prefix}sudo su${Font_color_suffix} 命令获取临时ROOT权限(执行后可能会提示输入当前账号的密码)。" && exit 1
|
||||
}
|
||||
function check_new_ver()
|
||||
{
|
||||
ct_new_ver=$(wget --no-check-certificate -qO- -t2 -T3 https://api.github.com/repos/ginuerzh/gost/releases/latest| grep "tag_name"| head -n 1| awk -F ":" '{print $2}'| sed 's/\"//g;s/,//g;s/ //g;s/v//g')
|
||||
if [[ -z ${ct_new_ver} ]]; then
|
||||
ct_new_ver="2.11.1"
|
||||
echo -e "${Error} gost 最新版本获取失败,正在下载v${ct_new_ver}版"
|
||||
# read -e -p "请输入版本号 [ 格式 x.x.xx , 如 0.8.21 ] :" ct_new_ver
|
||||
#[[ -z "${ct_new_ver}" ]] && echo "取消..." && exit 1
|
||||
else
|
||||
echo -e "${Info} gost 目前最新版本为 ${ct_new_ver}"
|
||||
fi
|
||||
}
|
||||
function check_file()
|
||||
{
|
||||
if test ! -d "/usr/lib/systemd/system/";then
|
||||
`mkdir /usr/lib/systemd/system`
|
||||
`chmod -R 777 /usr/lib/systemd/system`
|
||||
fi
|
||||
}
|
||||
function check_nor_file()
|
||||
{
|
||||
`rm -rf "$(pwd)"/gost`
|
||||
`rm -rf "$(pwd)"/gost.service`
|
||||
`rm -rf "$(pwd)"/config.json`
|
||||
`rm -rf /etc/gost`
|
||||
`rm -rf /usr/lib/systemd/system/gost.service`
|
||||
`rm -rf /usr/bin/gost`
|
||||
}
|
||||
function Install_ct()
|
||||
{
|
||||
check_root
|
||||
check_nor_file
|
||||
Installation_dependency
|
||||
check_file
|
||||
check_sys
|
||||
check_new_ver
|
||||
`rm -rf gost-linux-"$bit"-"$ct_new_ver".gz`
|
||||
`wget --no-check-certificate https://github.com/ginuerzh/gost/releases/download/v"$ct_new_ver"/gost-linux-"$bit"-"$ct_new_ver".gz`
|
||||
`gunzip gost-linux-"$bit"-"$ct_new_ver".gz`
|
||||
`mv gost-linux-"$bit"-"$ct_new_ver" gost`
|
||||
`mv gost /usr/bin/gost`
|
||||
`chmod -R 777 /usr/bin/gost`
|
||||
`wget --no-check-certificate https://raw.githubusercontent.com/KANIKIG/EasyGost/master/gost.service && chmod -R 777 gost.service && mv gost.service /usr/lib/systemd/system`
|
||||
`mkdir /etc/gost && wget --no-check-certificate https://raw.githubusercontent.com/KANIKIG/EasyGost/master/config.json && mv config.json /etc/gost && chmod -R 777 /etc/gost`
|
||||
`systemctl enable gost && systemctl restart gost`
|
||||
echo "------------------------------"
|
||||
if test -a /usr/bin/gost -a /usr/lib/systemctl/gost.service -a /etc/gost/config.json;then
|
||||
echo "gost安装成功"
|
||||
`rm -rf "$(pwd)"/gost`
|
||||
`rm -rf "$(pwd)"/gost.service`
|
||||
`rm -rf "$(pwd)"/config.json`
|
||||
else
|
||||
echo "gost没有安装成功,可以在Github[EasyGost]中提交issue"
|
||||
`rm -rf "$(pwd)"/gost`
|
||||
`rm -rf "$(pwd)"/gost.service`
|
||||
`rm -rf "$(pwd)"/config.json`
|
||||
`rm -rf "$(pwd)"/gost.sh`
|
||||
fi
|
||||
}
|
||||
function Uninstall_ct()
|
||||
{
|
||||
`rm -rf /usr/bin/gost`
|
||||
`rm -rf /usr/lib/systemd/system/gost.service`
|
||||
`rm -rf /etc/gost`
|
||||
`rm -rf "$(pwd)"/gost.sh`
|
||||
echo "gost已经成功删除"
|
||||
}
|
||||
function Start_ct()
|
||||
{
|
||||
`systemctl start gost`
|
||||
echo "已启动"
|
||||
}
|
||||
function Stop_ct()
|
||||
{
|
||||
`systemctl stop gost`
|
||||
echo "已停止"
|
||||
}
|
||||
function Restart_ct()
|
||||
{
|
||||
`systemctl restart gost`
|
||||
echo "已重启"
|
||||
}
|
||||
function read_protocol()
|
||||
{
|
||||
echo -e "请问您要设置哪种转发: "
|
||||
echo -e "-----------------------------------"
|
||||
echo -e "[1] tcp+udp流量转发, 不加密"
|
||||
echo -e "说明: 一般设置在国内中转机上"
|
||||
echo -e "-----------------------------------"
|
||||
echo -e "[2] 加密隧道流量转发"
|
||||
echo -e "说明: (1)用于转发原本加密等级较低的流量, 一般设置在国内中转机上"
|
||||
echo -e " (2)选择此协议意味着你还有一台机器用于接收此加密流量, 之后须在那台机器上配置协议[3]进行对接"
|
||||
echo -e "-----------------------------------"
|
||||
echo -e "[3] 解密由gost传输而来的流量并转发"
|
||||
echo -e "说明: 对于经由gost加密中转的流量, 通过此选项进行解密并转发给本机的代理服务端口或转发给其他远程机器, 一般设置在用于接收中转流量的国外机器上"
|
||||
echo -e "-----------------------------------"
|
||||
read -p "请选择转发方式: " numprotocol
|
||||
|
||||
if [ "$numprotocol" = "1" ]; then
|
||||
flag_a="nonencrypt"
|
||||
elif [ "$numprotocol" = "2" ]; then
|
||||
encrypt
|
||||
elif [ "$numprotocol" = "3" ]; then
|
||||
decrypt
|
||||
else
|
||||
echo "type error, please try again"
|
||||
exit
|
||||
fi
|
||||
}
|
||||
function read_s_port()
|
||||
{
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "请问你要将本机哪个端口接收到的流量进行转发?"
|
||||
read -p "请输入: " flag_b
|
||||
}
|
||||
function read_d_ip()
|
||||
{
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "请问你要将本机从${flag_b}接收到的流量转发向哪个IP或域名?"
|
||||
echo -e "注: IP既可以是[远程机器/当前机器]的公网IP, 也可是以本机本地回环IP(即127.0.0.1)"
|
||||
echo -e " 具体IP地址的填写, 取决于接收该流量的服务正在监听的IP(详见: https://github.com/KANIKIG/EasyGost)"
|
||||
read -p "请输入: " flag_c
|
||||
}
|
||||
function read_d_port()
|
||||
{
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "------------------------------------------------------------------"
|
||||
echo -e "请问你要将本机从${flag_b}接收到的流量转发向${flag_c}的哪个端口?"
|
||||
read -p "请输入: " flag_d
|
||||
}
|
||||
function writerawconf()
|
||||
{
|
||||
echo $flag_a"/"$flag_b"#"$flag_c"#"$flag_d >> $raw_conf_path
|
||||
}
|
||||
function rawconf()
|
||||
{
|
||||
read_protocol
|
||||
read_s_port
|
||||
read_d_ip
|
||||
read_d_port
|
||||
writerawconf
|
||||
}
|
||||
function eachconf_retrieve()
|
||||
{
|
||||
d_server=${trans_conf#*#}
|
||||
d_port=${d_server#*#}
|
||||
d_ip=${d_server%#*}
|
||||
flag_s_port=${trans_conf%%#*}
|
||||
s_port=${flag_s_port#*/}
|
||||
is_encrypt=${flag_s_port%/*}
|
||||
}
|
||||
function confstart()
|
||||
{
|
||||
echo "{
|
||||
\"Debug\": true,
|
||||
\"Retries\": 0,
|
||||
\"ServeNodes\": [" >> $gost_conf_path
|
||||
}
|
||||
function multiconfstart()
|
||||
{
|
||||
echo " {
|
||||
\"Retries\": 0,
|
||||
\"ServeNodes\": [" >> $gost_conf_path
|
||||
}
|
||||
function conflast()
|
||||
{
|
||||
echo " ]
|
||||
}" >> $gost_conf_path
|
||||
}
|
||||
function multiconflast()
|
||||
{
|
||||
if [ $i -eq $count_line ]; then
|
||||
echo " ]
|
||||
}" >> $gost_conf_path
|
||||
else
|
||||
echo " ]
|
||||
}," >> $gost_conf_path
|
||||
fi
|
||||
}
|
||||
function encrypt()
|
||||
{
|
||||
echo -e "请问您要设置的转发传输类型: "
|
||||
echo -e "-----------------------------------"
|
||||
echo -e "[1] tls"
|
||||
echo -e "[2] ws"
|
||||
echo -e "[3] wss"
|
||||
echo -e "注意: 同一则转发,中转与落地传输类型必须对应!本脚本默认开启tcp+udp"
|
||||
echo -e "-----------------------------------"
|
||||
read -p "请选择转发传输类型: " numencrypt
|
||||
|
||||
if [ "$numencrypt" = "1" ]; then
|
||||
flag_a="encrypttls"
|
||||
elif [ "$numencrypt" = "2" ]; then
|
||||
flag_a="encryptws"
|
||||
elif [ "$numencrypt" = "3" ]; then
|
||||
flag_a="encryptwss"
|
||||
else
|
||||
echo "type error, please try again"
|
||||
exit
|
||||
fi
|
||||
}
|
||||
function decrypt()
|
||||
{
|
||||
echo -e "请问您要设置的解密传输类型: "
|
||||
echo -e "-----------------------------------"
|
||||
echo -e "[1] tls"
|
||||
echo -e "[2] ws"
|
||||
echo -e "[3] wss"
|
||||
echo -e "注意: 同一则转发,中转与落地传输类型必须对应!本脚本默认开启tcp+udp"
|
||||
echo -e "-----------------------------------"
|
||||
read -p "请选择解密传输类型: " numdecrypt
|
||||
|
||||
if [ "$numdecrypt" = "1" ]; then
|
||||
flag_a="decrypttls"
|
||||
elif [ "$numdecrypt" = "2" ]; then
|
||||
flag_a="decryptws"
|
||||
elif [ "$numdecrypt" = "3" ]; then
|
||||
flag_a="decryptwss"
|
||||
else
|
||||
echo "type error, please try again"
|
||||
exit
|
||||
fi
|
||||
}
|
||||
function method()
|
||||
{
|
||||
if [ $i -eq 1 ]; then
|
||||
if [ "$is_encrypt" = "nonencrypt" ]; then
|
||||
echo " \"tcp://:$s_port/$d_ip:$d_port\",
|
||||
\"udp://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encrypttls" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+tls://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encryptws" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+ws://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encryptwss" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+wss://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decrypttls" ]; then
|
||||
echo " \"relay+tls://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decryptws" ]; then
|
||||
echo " \"relay+ws://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decryptwss" ]; then
|
||||
echo " \"relay+wss://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
else
|
||||
echo "config error"
|
||||
fi
|
||||
elif [ $i -gt 1 ]; then
|
||||
if [ "$is_encrypt" = "nonencrypt" ]; then
|
||||
echo " \"tcp://:$s_port/$d_ip:$d_port\",
|
||||
\"udp://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encrypttls" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+tls://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encryptws" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+ws://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "encryptwss" ]; then
|
||||
echo " \"tcp://:$s_port\",
|
||||
\"udp://:$s_port\"
|
||||
],
|
||||
\"ChainNodes\": [
|
||||
\"relay+wss://$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decrypttls" ]; then
|
||||
echo " \"relay+tls://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decryptws" ]; then
|
||||
echo " \"relay+ws://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
elif [ "$is_encrypt" = "decryptwss" ]; then
|
||||
echo " \"relay+wss://:$s_port/$d_ip:$d_port\"" >> $gost_conf_path
|
||||
else
|
||||
echo "config error"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
function writeconf()
|
||||
{
|
||||
count_line=$(awk 'END{print NR}' $raw_conf_path)
|
||||
for((i=1;i<=$count_line;i++))
|
||||
do
|
||||
if [ $i -eq 1 ]; then
|
||||
trans_conf=$(sed -n "${i}p" $raw_conf_path)
|
||||
eachconf_retrieve
|
||||
method
|
||||
elif [ $i -gt 1 ]; then
|
||||
if [ $i -eq 2 ]; then
|
||||
echo " ],
|
||||
\"Routes\": [" >> $gost_conf_path
|
||||
trans_conf=$(sed -n "${i}p" $raw_conf_path)
|
||||
eachconf_retrieve
|
||||
multiconfstart
|
||||
method
|
||||
multiconflast
|
||||
else
|
||||
trans_conf=$(sed -n "${i}p" $raw_conf_path)
|
||||
eachconf_retrieve
|
||||
multiconfstart
|
||||
method
|
||||
multiconflast
|
||||
fi
|
||||
fi
|
||||
done
|
||||
}
|
||||
function show_all_conf()
|
||||
{
|
||||
echo -e " GOST 配置 "
|
||||
echo -e "--------------------------------------------------------"
|
||||
echo -e "序号|方法\t |本地端口\t|目的地地址:目的地端口"
|
||||
echo -e "--------------------------------------------------------"
|
||||
|
||||
count_line=$(awk 'END{print NR}' $raw_conf_path)
|
||||
for((i=1;i<=$count_line;i++))
|
||||
do
|
||||
trans_conf=$(sed -n "${i}p" $raw_conf_path)
|
||||
eachconf_retrieve
|
||||
|
||||
if [ "$is_encrypt" = "nonencrypt" ]; then
|
||||
str="tcp+udp不加密"
|
||||
elif [ "$is_encrypt" = "encrypttls" ]; then
|
||||
str="tls隧道"
|
||||
elif [ "$is_encrypt" = "encryptws" ]; then
|
||||
str="ws隧道"
|
||||
elif [ "$is_encrypt" = "encryptwss" ]; then
|
||||
str="wss隧道"
|
||||
elif [ "$is_encrypt" = "decrypttls" ]; then
|
||||
str="tls解密"
|
||||
elif [ "$is_encrypt" = "decryptws" ]; then
|
||||
str="ws解密"
|
||||
elif [ "$is_encrypt" = "decryptwss" ]; then
|
||||
str="wss解密"
|
||||
fi
|
||||
|
||||
echo -e " $i |$str |$s_port\t|$d_ip:$d_port"
|
||||
echo -e "--------------------------------------------------------"
|
||||
done
|
||||
}
|
||||
echo && echo -e " gost 一键安装配置脚本
|
||||
----------- KANIKIG -----------
|
||||
特性: (1)本脚本采用systemd及gost配置文件对gost进行管理
|
||||
(2)能够在不借助其他工具(如screen)的情况下实现多条转发规则同时生效
|
||||
(3)机器reboot后转发不失效
|
||||
功能: (1)tcp+udp不加密转发, (2)中转机加密转发, (3)落地机解密对接转发
|
||||
帮助文档:
|
||||
|
||||
${Green_font_prefix}1.${Font_color_suffix} 安装 gost
|
||||
${Green_font_prefix}2.${Font_color_suffix} 更新 gost
|
||||
${Green_font_prefix}3.${Font_color_suffix} 卸载 gost
|
||||
————————————
|
||||
${Green_font_prefix}4.${Font_color_suffix} 启动 gost
|
||||
${Green_font_prefix}5.${Font_color_suffix} 停止 gost
|
||||
${Green_font_prefix}6.${Font_color_suffix} 重启 gost
|
||||
————————————
|
||||
${Green_font_prefix}7.${Font_color_suffix} 新增gost转发配置
|
||||
${Green_font_prefix}8.${Font_color_suffix} 查看现有gost配置
|
||||
${Green_font_prefix}9.${Font_color_suffix} 删除一则gost配置
|
||||
————————————" && echo
|
||||
read -e -p " 请输入数字 [1-9]:" num
|
||||
case "$num" in
|
||||
1)
|
||||
Install_ct
|
||||
;;
|
||||
2)
|
||||
checknew
|
||||
;;
|
||||
3)
|
||||
Uninstall_ct
|
||||
;;
|
||||
4)
|
||||
Start_ct
|
||||
;;
|
||||
5)
|
||||
Stop_ct
|
||||
;;
|
||||
6)
|
||||
Restart_ct
|
||||
;;
|
||||
7)
|
||||
rawconf
|
||||
rm -rf /etc/gost/config.json
|
||||
confstart
|
||||
writeconf
|
||||
conflast
|
||||
`systemctl restart gost`
|
||||
echo -e "配置已生效,当前配置如下"
|
||||
echo -e "--------------------------------------------------------"
|
||||
show_all_conf
|
||||
;;
|
||||
8)
|
||||
show_all_conf
|
||||
;;
|
||||
9)
|
||||
show_all_conf
|
||||
read -p "请输入你要删除的配置编号:" numdelete
|
||||
sed -i "${numdelete}d" $raw_conf_path
|
||||
rm -rf /etc/gost/config.json
|
||||
confstart
|
||||
writeconf
|
||||
conflast
|
||||
`systemctl restart gost`
|
||||
echo -e "配置已删除,服务已重启"
|
||||
;;
|
||||
*)
|
||||
echo "请输入正确数字 [1-9]"
|
||||
;;
|
||||
esac
|
||||
Reference in New Issue
Block a user